This blog post is more than five years old. It may contain outdated information or refer to products that are no longer available.
As nonprofits transition to a remote workforce during the COVID-19 pandemic, significant changes to the traditional IT systems at most organizations are afoot. Meetings have gone virtual, staff are using both work and personal devices, and nearly everyone is connecting to the Internet on their home Wi-Fi networks. Along with all this comes new security concerns that nonprofits must keep in mind to keep their systems safe.
This post contains some important considerations for your nonprofit during these times, but they are are also important no matter the circumstance. Much of this is drawn directly from our recent webinar, Keeping Your Nonprofit's Systems Secure While Working Remotely. You can find a recording of this webinar below.
The webinar's one major takeaway was that implementing security measures is important to organizations of all sizes because hackers who want to capitalize on the current situation are attacking a wide range of targets indiscriminately. To that end, most of the solutions we're pointing to here are relatively low-cost and possible to implement with little to no IT support. We also encourage nonprofits to invest in the paid — not free — versions of any of these tools since these will be the most secure and effective in the long run.
And with that, let's focus on how to keep your nonprofit's systems safe during the COVID-19 pandemic.
Cyber Threats We're Seeing
One of the primary ways computers and systems are being hacked is via fake emails that entice you to take some action like clicking on a link or downloading and opening an attachment (called phishing). Other methods include fake online ads on social media, websites, or browser pop-ups that can install malware when clicked on (sometimes referred to as malware clickbait).
Phishing Examples
Phishing emails are designed to trick an unsuspecting person into providing sensitive information that can give them access to both organizational and personal data — TechSoup and Tech Impact staff have been receiving phishing emails daily over the last several weeks.
Some are fairly obvious, like the one below:
If you look closely at the email above, there are a few things that suggest it is a phishing attempt. The first sign is that the email references Office 365 but does not come from either Microsoft or a legitimate company that offers Microsoft services. The content itself is also suspicious because there are typos and it uses an unknown email ID.
Others are a bit sneakier, in which hackers try to pose as someone within your organization. In this case, the hacker used a custom field to pose as an HR staff member asking the recipient to click through to a required training.
Hackers use publicly available information on websites, including your own nonprofit website, to identify key information that can be used to trick you, such as your email domain and senior staff names. The email above actually looks like it is coming from your HR manager, and the individual's name may even be spoofed in the From field of the email and the content of the email. However, if you look at the actual From email address, you will notice that it does not actually come from that individual. Always be suspicious of an email coming from your CEO, HR, or others if there is a request for action of any kind. It can be a phishing attempt.
There are many COVID-19-related phishing and other types of scams out there right now, trying to get you to provide access to sensitive data or separate you from your money.
App scams: Scammers are also creating and manipulating mobile apps designed to track the spread of COVID-19 to insert malware that will compromise users' devices and personal information.
Charity scams: Scammers are soliciting donations for individuals, groups, and areas affected by COVID-19.
Treatment scams: Scammers are offering to sell fake cures, vaccines, and advice on unproven treatments for COVID-19. Scammers are also posing as national and global health authorities, including the World Health Organization (WHO) and the Centers for Disease Control and Prevention (CDC), tricking recipients into downloading malware or providing personal identifying and financial information.
Supply scams: Scammers are creating fake shops, websites, social media accounts, and email addresses claiming to sell medical supplies currently in high demand, such as surgical masks. When consumers attempt to purchase supplies through these channels, fraudsters pocket the money and never provide the promised supplies.
Provider scams: Scammers are also contacting people by phone and email, pretending to be doctors and hospitals that have treated a friend or relative for COVID-19 and demanding payment for that treatment.
Investment scams: Scammers are offering online promotions on various platforms, including social media, claiming that the products or services of publicly traded companies can prevent, detect, or cure COVID-19, and that the stock of these companies will dramatically increase in value as a result.
COVID-19-specific scams: There is a lot of phishing activity related to COVID-19 that asks people to provide information in order to access benefits or information. These are examples highlighted by KnowBe4:
- Coronavirus Stimulus Package (SSN): Claims that the person is eligible for a $1,200 stimulus check, and they just need to enter their Social Security number to confirm.
- Coronavirus Testing Kit (SSN): Claims that due to new government regulation, the person can receive a free coronavirus testing kit sent to their home.
- Coronavirus School Schedule (SSN): Targets parents by referencing a change in their child's school schedule due to the coronavirus, then asks for the Social Security number to confirm identity.
- Increased Coronavirus Cases in Your Area (zip code): A call from the local "county commissioner" claims that there has been an increase in coronavirus cases in their area and requests their zip code to confirm their location.
The best way to protect yourself and your organization against phishing threats is to train your staff to be aware that they exist and to know how to spot and report them as they come in. One great way to do this is to have staff take an online course in cybersecurity such as KnowBe4 (more on this below). Remember, it is always better to err on the side of caution and treat all email as potentially dangerous.
Malware Clickbait
Cybersecurity researchers have identified several fake COVID-19 tracker maps like the one below that infect people's computers with embedded malicious code when you click on the image to open it. The tactic is one of many ways hackers and scammers are capitalizing on people's fears about COVID-19 to spread malware.
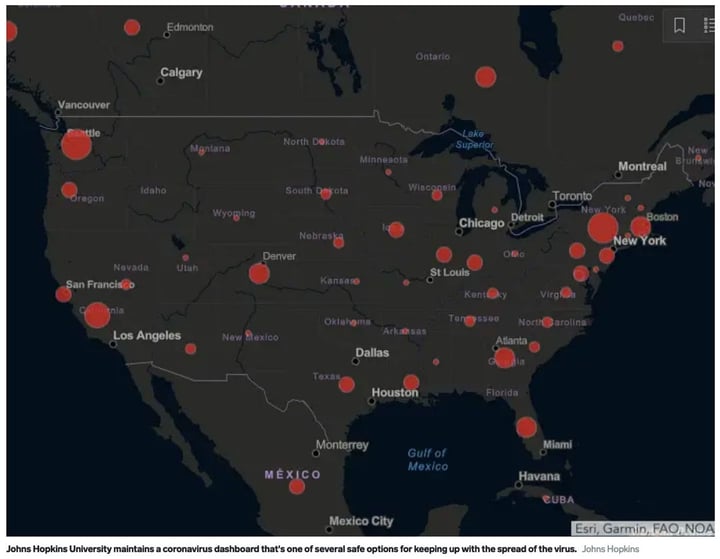
In general, never click on an image in an ad or email or follow a link unless you verify that it is legitimate. An image is only safe if you recognize and trust the sender. This is true with websites as well, and it is always prudent to validate the URL you're clicking on and check that it is secure, with a reputable certificate. You can check the certificate easily by clicking on the lock symbol next to the URL. In most browsers, if you see a red line through the lock, this indicates the site is not secure and may contain malware.
How to Stay Safe at Your Nonprofit
Given the multitude of threats that exist, you may be overwhelmed by the prospect of protecting yourself against hackers while doing your best to keep everything else at your organization up and running. But there are a number of measures you can take to greatly improve your IT security.
Best Practices to Follow
Here are some simple best practices to keep in mind, regardless of whether you have a remote workforce or you've returned to your office:
- Only open email from known email addresses (always check the email address twice).
- If something looks suspicious, check with your management team, HR, or IT team (if you have one) before clicking any links. Use phone or chat to verify. Don't reply to the email to check.
- Office 365 and Google for Nonprofits Gmail can be configured by your IT pro to prevent these emails from coming through to your inbox.
- Never click a link or attachment in an email unless you know what it is and who it is from.
- Only get your news from trusted sources such as reputable news sites, official government websites (with the .gov domains), or sites with security certificates.
- Always be aware of who you are following on social media and be thoughtful before clicking links to those cute dog videos or COVID-19 live tracking maps.
- Know who built that COVID-19 mobile app before you download — only get COVID-19 apps from health departments, hospitals, and trusted sources.
- Never save organization passwords in your browser on your home computer.
- Don't store confidential data on your home computer.
- When in doubt, don't click the link. Contact the sender by other means, like the phone.
Harden Your Home Computers and Networks
It's always better to use devices managed by your organization. But in the event your staff must use personal computers while working from home, here are some tips on how to better secure personal computers and home networks, including using a VPN or remote desktop (or both — more on that in a bit).
Computer Hardware
Ensure that all available updates are applied to all applications running on that computer, including
- Windows or Mac operating system security patches and updates
- Firefox, Chrome, or other browser updates
- Office productivity suite updates (Word, Outlook, etc.)
- Other applications, such as those from Adobe, Zoom, and Slack
Also be sure that you're running a fully up-to-date version of antivirus software and that it is scheduled to regularly scan your device. For Microsoft and Office 365 users, Windows Advanced Threat Protection (ATP) or Windows Defender are great solutions. But other powerful antivirus solutions, including those from Bitdefender and NortonLifeLock provide excellent protection against malware and other threats. All of these are available through TechSoup.
Home Network Security
There are a few simple steps you can take to better secure your home Wi-Fi network:
- Make sure your router and Wi-Fi system are not using the default passwords.
- Hide your SSID by configuring your system to not broadcast it.
- Some systems allow you to have a "guest" network so you can separate your work traffic from the rest of your family's traffic.
- For extra protection, configure your router and Wi-Fi system to only allow approved devices on the network.
- For information on how to configure these settings for your router and Wi-Fi system, consult the documentation for your specific system.
Other Basic Cybersecurity Tips
Here are a few more actions to consider that will keep your organization more secure. Again, these aren't just security measures to implement during this crisis — they're widely adopted practices that you should consider no matter the circumstance.
- Use multi-factor authentication (MFA). MFA provides an extra layer of security when user credentials have been compromised by bad actors. MFA requires an extra identity check to authenticate your login credentials by asking you to provide something that you know, such as an answer to a specific question (like what color was the house you grew up in) or cross-checking your identity by texting a code to your mobile phone. Most applications have this feature or they use an app like Google's Authenticator.
- Use single sign-on (SSO) to allow staff to access all your cloud systems with one password that is managed by the organization. Organizations that use Microsoft 365 and Office 365 can leverage Azure Active Directory Federation Services (ADFS) to synchronize organization account credentials with other applications using SSO protocols. It is also possible to leverage cloud-based identity management solutions such as Okta.
- Communicate clearly with remote workers. Send best practices, security alerts, and updates as soon as they become available.
Virtual Private Networks and Remote Desktops
VPNs and remote desktop clients are advanced security measures that you should seriously consider using. However, it should be noted that each of these should only be implemented by an IT professional.
Companies employ the use of a VPN system to ensure that employees who are remote can access resources behind the company's firewall securely. Importantly, it also encrypts all data that is passed from your computer to the services you are connecting to. This adds an additional layer of security even when you are not accessing your company's information systems directly.
TechSoup offers Cisco Meraki security appliances that let you set up VPNs.
Organizations can also provide access to desktops in the office using a remote desktop client (RDC). RDC software allows a user to log in remotely to another desktop system to access on-premises applications on office computers. Nonprofits often have accounting software like QuickBooks, client management systems, or donor databases installed on computers in the office. Examples of RDC software include
- LogMeIn
- TeamViewer (available through TechSoup)
- GoToMyPC
Note: Do not use any of the free remote desktop clients that you can find on the Internet. These can pose a security risk.
It is very important to only set up an RDC under the guidance of your IT department because the configuration must be done correctly. In all cases, access must be protected by a firewall, and the service must only be used over a VPN. Otherwise, it can open up a vulnerability in your network because hackers scan to find unprotected services like this in networks. This is particularly true in times like these when hackers are in overdrive mode looking for ways to exploit openings.
Train Your Staff
All of the above is valuable information that should be shared with your staff, and implementing these solutions alone will increase your organization's IT security a great deal. But because human error can undo even the best security setups, the next step to truly protecting your nonprofit is to implement formal cybersecurity training.
KnowB4 Security Awareness Training and discounted rates are offered to nonprofits via the TechSoup catalog. (Full disclosure: TechSoup uses this platform, and all of our staff were put through a refresher training as we transitioned to remote work in early March.) The platform provides numerous online training modules, from introductory IT security basics to more advanced topics that might better fit an organization's specific needs. All sessions are extremely interactive and are geared toward changing employees' online behavior in order to promote better cybersecurity.
We hope that all of this has given you and your organization some clarity and direction as to what can be done to keep your systems safe during these difficult times. If you have any tips you'd like to share or questions you'd like to pose to the community, be sure to check out TechSoup's COVID-19 forum. It's full of useful information, and it's a great way to connect with other organizations like yours.
Additional Resources
- See TechSoup's directory of Resources for Nonprofits Impacted by COVID-19.
- Read more security-related blog posts.
- Check out TechSoup Courses' free learning track to support nonprofits during the COVID-19 pandemic.






